Latebra 2.0
Now when a lot of organizations and persons try to infringe your privacy, the privacy protection became actual task.
This task is solved by Latebra which creates “ecosystem” to exchange by confidential E-mail/ SMS/ MMS messages and to be not afraid that somebody can read it. Latebra encrypts and protects your contact date even if your phone (or tablet) was stolen.
You can download this App here:
Latebra encrypts and decrypts correspondence ( any kind of messages SMS/MMS/Email) by own original cipher algorithm. This algorithm is unknown in the world and hence it is not target of main hacker groups.
The encrypted procedure of Latebra is classified as end-to end encryption that means all processes of crypto key generation and decryption performs on users devices. Outside services, which can be disloyal to you or hacked don’t use for these tasks.
Users of Latebra distribute personal crypto keys to create closed “ecosystems” where only accepted persons can read correspondence intended for them. Nobody can read alien e-mails and sms.
Latebra encrypts contact data to protect their from unauthorized access. Nobody uses your contact data even if your phone (or tablet) was stolen.
Two type of crypto keys uses in Latebra. The one type (App key) provides access to Latebra and contact data encryption. Only you as owner of Latebra know codeword to access into Latebra and can restore and change this crypto key.
The second type (personal crypto keys) is used for message encryption when each correspondent is previously assigned own crypto key. A personal crypto key can be generated and assigned to some person; this key with message has to be sent to this person as addressee and be opened by him. It will assign this crypto key to the sender and in this case these persons can start exchange by encrypted messages which will be encrypted /decrypted by automatically choosing of the needed crypto key.
| 1. The usage of different crypto keys for message encryption and access to Latebra and contact data encryption.
2. Effective and easy distribution of crypto-keys.
3. The original guaranteed cipher algorithm using long length crypto-keys.
4. End-to end encryption (the message encryption and the generation of crypto-keys are performed on users’ gadgets).
5. The encryption/decryption of all kind of messages: SMS, email and contact data.
6. Each correspondent can has own crypto key which assigned to him only.
7. The unified messaging environment provides: viewing, deleting, creating, editing and encryption/decryption messages with automatic choice of crypto-key for encryption.
NOT NECESSARY TO REMEMBER WHICH CRYPTO-KEY IS USED FOR ENCRYPTION OF MESSAGES FROM THE ADDRESSEE.
8. Direct connection to Google and Yandex accounts.
9. Support copy paste mode to work with other Internet services.
10. Inbuilt “Address book” integrated into messaging environment to facilitate input and synchronized with “Contacts” supports following functionality: generation and distribution of crypto-keys, viewing, searching, editing and encryption of contact data including the work with contact groups. |
- Interface in Material Design style.
- Optimization and acceleration of processes: encrypting/decrypting, searching, loading not only messages, but also contact data.
- Two independent kinds of crypto-keys, the one for encryption correspondence, the second for restriction access to Latebra and contact data encryption.
- Personal crypto-keys when each correspondent may has own key for encryption correspondence.
- Inbuilt “Address book” provides following functionalities: contact data encryption, generation and distribution of crypto keys.
1.Install Latebra.
2.Next step is generation of App crypto-key to provide access in Latebra and encryption of contact data. You have to invent a codeword (or a phrase), determine languages used in correspondence and set security level when you generate a crypto-key. Need remember that security will be more than the level will be set larger, but the encryption in this case will be slower.
Fig. 1 Process of crypto-key generation
Fig. 2 Access mode definitions
3.Set access mode in Latebra.
Our recommendation is definitely to use a code word to start work with Latebra and close the App after each session.
This setting can be changed always.
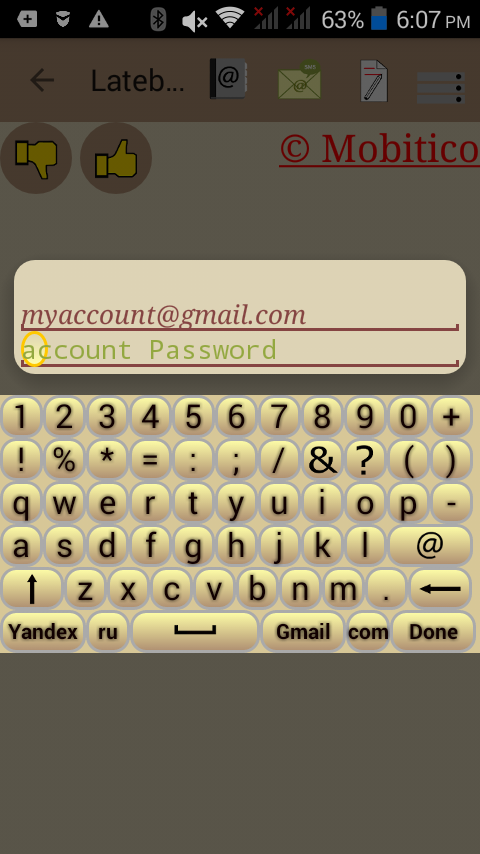
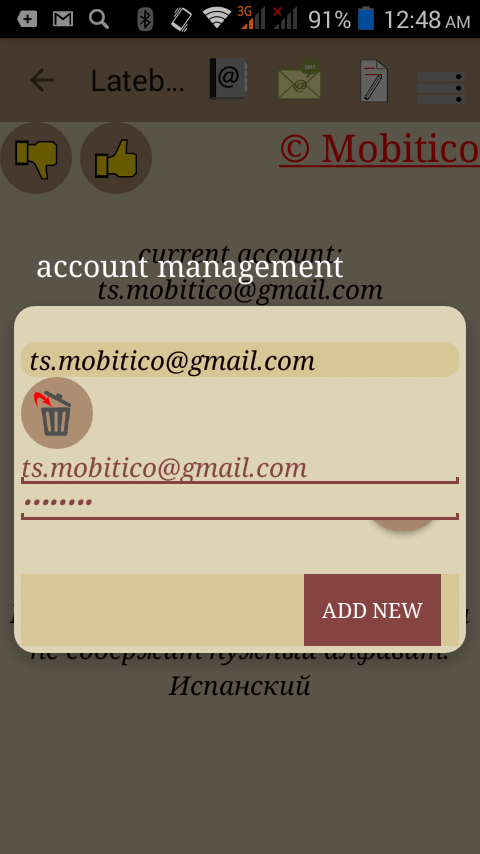
4. Connect Latebra to your E-mail accounts directly (Gmail or/and Yandex only) to use it as E-mail client with encryption functionality.
Don’t forget to turn on access to your account in Gmail for Latebra!!! It’s important. Latebra cannot work with Gmail without this permission.
Latebra will be SMS client only, if the similar connection will be not set. But in this caser you can work with Email using copy&paste procedures.
Fig. 3 Connecting an e-mail account
Fig. 4 Latebra main window
5. Item 4 finishes the preliminary setting. Hereafter all management of Latebra will be realized through main window.
If initial setup is finished, you can start to work with Latebra. Hereafter all management of Latebra will realize through main window to call up:
- Inbuilt “Address book” to encrypt, use, edit of contact data, generate and distribute personal crypto-key;
- The unified messaging support environment to load of received messages, view of loading messages list and activation of “Editor” for following work with selected message: viewing, decrypting, creating new, editing, encrypting and sending;
- “Editor” for fast creating, encrypting, and sending messages without preliminary loading of received messages;
- Settings of Latebra.
6. The click on the button “Address book” will open alphabetical contact list. Click on the snackbar “Filter“ to change active contact group. Here you can encrypt all contact data including photos which would like to keep in secret and then you have to save result
Fig. 5 List of contacts in the “Address book”
Fig. 6 List of encrypted contacts
They will show in the «Contacts» as encrypted and their usage standard ways will be impossible. But you can use them into Latebra without any problem.
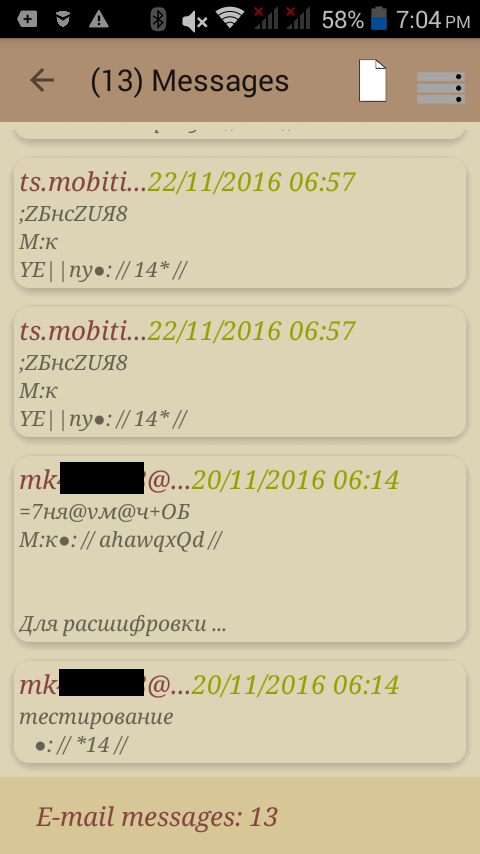
Select any contact from the list and click button “correspondence” you can see list of all messages which were sent or received from all E-mail addresses (phone numbers) of this person. It can be done even if his contact data previously were encrypted.
Fig. 7 The list of received messages
Fig. 8 Card of a particular contact
You can select any message from this message list and click needed button to delete it or view “chain” of messages received or sent (marked yellow) to the address (or phone number) the selected message. The “chain” can be deleted in one click.
Click on a contact in alphabetical contact list to open a “Contact Card” with a photo and contact data: phone numbers and E-mail addresses. These data can be encrypted all or partially directly in the “Contact Card”.
Each fields of a “Contact Card” are control elements. Click on “Name” to show personal crypto-key (if it exists for this contact). Click on “Phone numbers” to call the dialog:
- to the data edit;
- to Delete their;
- to call to selected phone number;
- to send SMS/MMS message to the person with this number.
Click on “Email” to call similar dialog to edit or delete data or to send Email to the selected address.
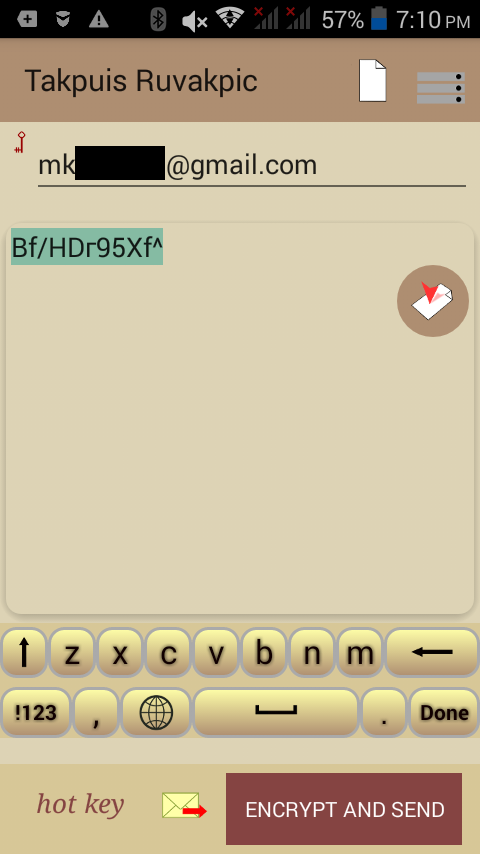
When you select the option to send message, it calls the Editor for typing, encrypting and sending a message.
There is special procedure in “Address book” to avoid in contact list of duplicate data.
Fig. 9 Editing the contact data
Fig. 10 Merging duplicate contact data
7.Click the button “Key” in a contact card to generate a personal crypto-key and send it. The distribution of crypto-keys can be done by e-mail or SMS messages. You have to generate of the set of unique personal crypto-keys, assign them to a persons with whom you are planning confidentially communicate and send these keys to these addressees. They have to have Latebra. It can be done one time but you can change keys in any time. When the message with crypto-key will be opened by the addressee, this key will be assigned to him and it means that you can safely exchange messages with him. It means that this addressee became member of your “circle of trust”.
The crypto-key generation and assigning can be done also directly in the Editor. You have to enter an address (number of mobile phone or Email address) and click the button “Key” on the Toolbar. In this case this key will be assigned to the contact with this address. Then you have to send the message with crypto-key to an addressee which has to open this message.
Everybody can create own “circle of trust” and invite you to come in it, if he sent to you a message with crypto-key. You become a member of “circle of trust” when you opened this message and hence crypto-key assigned to you.
We recommend delete the message with crypto-key after it was opened and the key was assigned.
Fig.11 Editor window with received message
When crypto-keys were generated, distributed and assigned the persons it means that you can easy exchange encrypted messages with them. Latebra will select the needed crypto-key for encryption automatically and there isn’t necessity to remember their, because Latebra knows which the key has to be used.
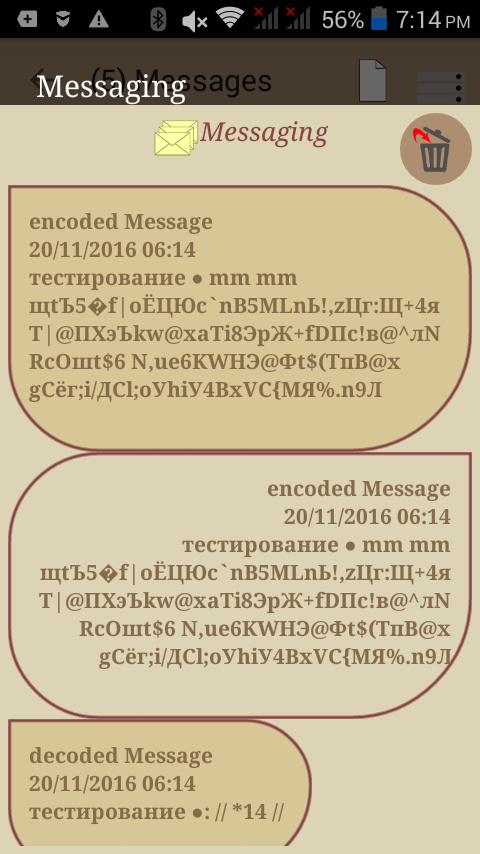
8.Click on the button “Message” to load messages in Latebra. Only users of Gmail and Yandex can work with Latebra effectively, Latebra will be Email client with encryption/decryption functionality for them. Users of other Email services can work with Latebra uses only copy&paste mode. They cannot load messages into Latebra directly.
The work with messages starts with the selection kind of messages Fig. 8, and then you have to click the button “next” to load messages in accordance with filter condition.
Fig. 12 Message type selection filter
Click on any message in message list to select it for following action:
- To load selected message into Editor for viewing, encrypting/decrypting sending and responding;
- To view message chain (sent messages have dark background) with addressee of selected message;
- To delete selected message
You can create and send a new message by click on action button “New” and manage E-mail accounts by click on the button “Account Management“.
Any message from the list can be selected and then can be done following actions: 1) delete, 2) open in “Editor”, 3) view “chain” of all messages from the addressee which sent this message. There is the alternative variant to see all correspondence from any addressee through “Address book” where you have to select interesting address and click the button “Correspondence”.
Fig. 14 Editor window with encrypted text
“Editor” is needed for performing main action with alone message, such as viewing, decrypting, creating, editing, encrypting and sending. Also “Editor” may be used for crypto –keys generation, sending and assigning these keys.
9.There is special button in main window of Latebra for fast call up “Editor”.
It provides possibility to create and send new Emails without preliminary loading others Emails, it became important when speed of Internet is low.
The Editor can be called up also by 2 other ways:
1) Click on selected message in list of messages and load it into the Editor.
2) Click on the button “New” and call up the Editor where you can create, encrypt and send a new message.
The Editor provides following functionality:
- viewing;
- creating and editing, including pasting of text from clipboard;
- encrypting/decrypting;
- saving;
- sending of messages;
- generation crypto-keys directly inside Editor; it can be done by just click on the button “Golden key”.
10.Initial setup in any time can be changed by click on the button “Settings” . Settings provide following functionalities:
A) checking connected E-mail account parameters or creating a new connection;
B) generation a new App crypto-key;
C) restoring previous App crypto-key if you remember previous codeword and approximate time of generation.
Item A) can be fulfilled only if you are Gmail or Yandex user.
Remember: after App crypto-key changing all things earlier encrypted are impossible to decrypt. We recommend decrypting all before App crypto-key changing.
If you forgot these recommendations you can temporary restore App crypto-key by using corresponding codeword and then decrypt all things needful.
Fig. 16 Account management
Android Version 4.0 for all devices phones/tablets and higher.
Adapted for tablets